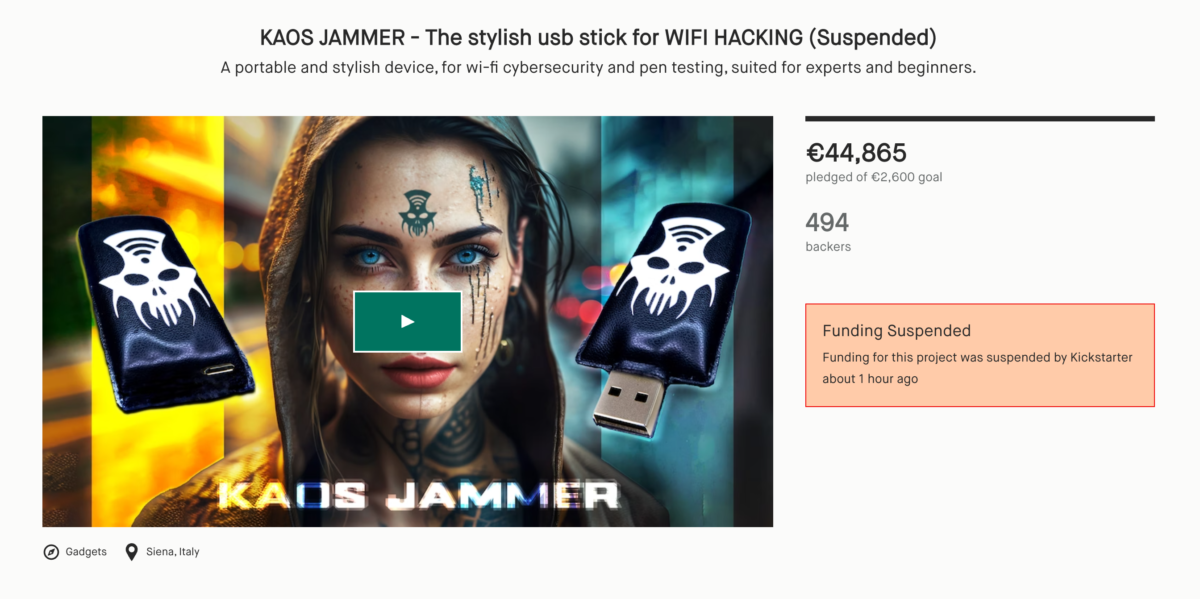
From KICKSTARTER to the SUCCESS to YOU ?
Over 800 backers already pledge from this store
We overpass Kickstar backers, And this is All Thanks to You. Kaos is Coming..
updated at 21 – Dicember – 2023
Since KICKSTARTER decide to suspend Our Project, thanks to your interest and support we decide to make Our Own Crowfunding Presale Platform.
The Future of KAOS JAMMER is in Your Hands.. Now more than ever we need your support to make KAOS JAMMER a reality.
Please JOIN our MAILINGLIST and our SOCIALS to let us keep you updated about new products, promo and maybe new suspensions.
CHOOSE WISELY
GET YOURS NOW – THIS OFFERTS IS TIME LIMITED
SEEN ON
Translation may contain mistranslations
Story


INTRO – DESCRIPTION
KAOS JAMMER is a portable device for hackers, geeks and cybersecurity professionals that looks like a normal USB storage drive, but is a cutting-edge cybersecurity tool that has been designed to provide users with a complete pack of Wi-Fi based security tools. The compact design of this device allows it to be easily carried around. Despite its small size, the KJ packs powerful tools for exploiting vulnerabilities present in Wi-Fi networks.
KAOS JAMMER is a cool and handy tool for all tech-savvy people. It’s shaped like a USB pen and packed with all the tools you need for exploring and testing Wi-Fi systems. Highly customizable to your liking! KJ is not just functional, it’s also stylish and perfect for any kind of hacking and research.

The KAOS JAMMER has a unique and stylish design. It is wrapped in a soft and firm eco-leather, which is both durable and comfortable to hold. The device features a vinyl cut design that embodies the spirit of the cult. With its unique design, advanced functionality, and portability, the KJ is a tool that is truly unmatched in the world of cybersecurity.
KAOS JAMMER is the perfect device for those who wanna learn about hacking and cyber security professionals.
DESIGN

The soft eco-leather wrapping on the KAOS JAMMER provides a comfortable grip and a premium feel. The texture of the leather is soft to the touch and the firmness of the material adds to its durability. The user is able to experience a sense of control and comfort while holding the device, making it an enjoyable tool to use and cool to look at.



In addition to the eco-leather, the vinyl cut design adds to the overall tactile experience. The intricate design not only looks stylish, but it also provides a unique texture that sets it apart from other hacking devices. The user can feel the grooves and curves of the design, adding to the overall sensory experience of using the device.



Overall, the combination of the soft eco-leather and vinyl cut design create a tactile experience that is both comfortable and satisfying. The KAOS JAMMER not only serves its purpose as a “pen-testing” tool, but it is also stylish and provides a sensory experience that is unmatched in the world of cybersecurity.

VERSIONS
KAOS JAMMER comes in two versions: USB and Charge.

The “KAOS JAMMER USB” is ready to go, it just needs a USB wall socket or wall charger just for the electricity. It is not necessarily required to have a computer in order to activate the device; the device can be controlled through another device and connected to a USB port for power. It can be used with any plug, like for example: power bank, pc, laptop, usb charger etc. and then it can be controlled from any platform (cross-platform).

The “KAOS JAMMER USB” is a versatile device that can be powered through a range of USB-enabled power sources, including wall sockets, chargers, power banks, laptops, and PCs. Its universal compatibility with USB power sources ensures that it can be utilized with ease in any setting, without the need for specific equipment or cables. It can be controlled from any platform (cross-platform). So if you connect it on your laptop or a wall charger, it can be used via smartphone.

The “KAOS JAMMER Charge” is a powerful device, featuring a five DBI antenna for enhanced signal strength. This provides the user with the ability to cover a greater distance.

Additionally, the rechargeable lithium battery offers extreme portability, allowing the user to take the device wherever they go without worrying about running out of power or needing a power outlet.

Each of the models share the same software, with only one key difference: the “CHARGE” version features a stronger antenna and battery, providing enhanced capabilities compared to its counterpart.
*The image may suggest that the “KJ USB” device doesn’t have an antenna, but it HAS one just not as powerful as the one on the “KJ CHARGE” device.

ADDONS

Both the USB and Charge models of the KJ are compatible with the “Kaos Mobile Pack”, which allows the user to use or charge the device on the go using their cell phone. This pack will include all the adaptors needed to connect both models to any phone 8 units – usb c – micro usb – lightning – mini usb. (and some spares)

FEATURES

KJ can be utilized as a wireless signal strength analyzer, allowing for the assessment of Wi-Fi signal strength on the move. This feature is particularly useful for optimizing wireless network configurations room by room by selecting the optimal channel to minimize interference and achieve the best signal strength balance.
By utilizing the signal strength analysis capabilities of the KJ, users can make informed decisions about the placement of access points, antenna orientation, and channel selection, to name a few. These modifications can greatly improve the overall performance of a wireless network and ensure reliable, high-speed connections for all connected devices.

Since most standard routers rely on automatic channel selection, which most of the time is not the best configuration , KJ provides a hands-on approach to wireless network configuration. With the ability to actively analyze signal strength and make adjustments in real-time, users can ensure that their network is optimized for maximum performance at all times.

The KJ device operates as a wireless disruption tool, essentially functioning as a Wi-Fi deauthenticator. Its capabilities include scanning for both visible and concealed wireless networks, as well as identifying all connected devices. This device provides the capability to disrupt the connectivity of targeted devices or networks, either singularly or in bulk, by transmitting disconnection signals. Works with any wifi enabled device even drones, game consoles and wireless cameras.
KJ is designed for educational and testing purposes in the field of network security. It’s intended to simulate potential security threats and evaluate the resilience of Wi-Fi networks against such attacks.

KJ can be remote controlled through the Internet, thanks to the unique function. “Wi-fi Connect” that allows you to control all of the KJ functions from anywhere. KJ has mesmerizing animations and unique graphics to match with the look and feel of the device.
The KJ device features remote control capabilities via internet connectivity, through its proprietary “Wi-Fi Connect” function. This allows users to manage all functions of the device from a remote location. In addition to its remote control capabilities, the KJ device also includes various functionalities such as:

CROSS PLATFORM – MULTI ACCESS

One of the key advantages of the KJ is its cross-platform compatibility, allowing for seamless control and usage across a variety of operating systems and devices. For example, users can operate from any Electronics or Tech-wear, providing unparalleled flexibility and ease of use. The KJ offers a highly versatile and accessible solution, with compatibility across multiple platforms including iOS and Android,

through a dedicated mobile application. The device also features a web-based interface and a Web-APP, allowing for local or remote access and control from any device with a browser, including laptops, smartwatches, and a variety of operating systems, ensuring cross-platform functionality.

Even the Metaverse, we don’t know why you would do that.. but you can.
USER INTERFACE/EXPERIENCE – UX/UI

The device’s user interface (UI) is accompanied by captivating animations and distinctive graphics, providing a cohesive and aesthetically pleasing user experience (UX). In addition KJ provides a highly customizable experience, enabling users to personalize the interface to their individual preferences. With an extensive array of style combinations available, users can create a truly unique and personalized experience, tailored to their specific requirements.

The seamless and harmonious blend of aesthetics of the UI and the UX. Where form and function coexist in perfect balance. The carefully crafted design of the device is mirrored in its intuitive and responsive interface, elevating the overall look and feel of the device to new heights.

This smooth integration of aesthetics and UI showcases the attention to detail and commitment to excellence of the creation, and underscores the pressure to deliver a top-notch user experience.

The KJ has been designed with global appeal in mind, offering support for an extensive range of languages , over 50. This multilingual capability allows for a comprehensive user experience, regardless of the individual’s native language. By embracing diversity and catering to the needs of a global audience, the KJ truly stands out as a device that prioritizes the user’s experience.”

RESISTANCE – ENDURANCE

Water. No fear. KJ is highly durable. Drop proof made with hydrophobic and non-flammable materials. KJ is made to last.
The product is constructed with hydrophobic and non-flammable materials, ensuring durability and making it drop-proof. We are committed to creating a sustainable future and believe that the longevity of KJ is a crucial component of that vision.
We just want to make sure that you’re aware that our product is not intended for underwater use. We’re pretty sure you’re not planning on taking it scuba diving, but just in case, we want to emphasize that it’s not waterproof. So please keep your product on dry land!

That being said, we’ve taken steps to ensure that the internal chips are well-protected, so you don’t need to worry about accidental spills or splashes. However, if you do happen to submerge it in water, please be aware that it may not work as intended.
Also, just a heads up that the USB plug may be susceptible to rust if exposed to water or moisture for extended periods of time. We recommend keeping it dry to avoid any potential issues.

Finally, we want to note that any actions or statements made in our videos are intended for normal use of the product only. We don’t recommend attempting any crazy stunts or using it in ways that could be dangerous or harmful. Please use your product responsibly and enjoy it to its fullest potential!
VIDEO TUTORIALS – EDUCATIONAL

KJ includes educational videos that will show you how to use the device and teach you about the vulnerabilities of Wi-Fi systems.
KJ is more than just a product, it’s a commitment to educate the public about the critical importance of cybersecurity and Wi-Fi vulnerabilities. Unfortunately, these topics are often seen as complicated and are frequently ignored, leading to poor choices and a lack of knowledge about the potential risks of an attack. This is why the average user tends to take many unnecessary risks, and sensibility in the field of cybersecurity has stagnated. That’s why the educational component of the KJ project is so important. The included educational videos not only show you how to use the device effectively, but they also provide valuable information about the vulnerabilities of Wi-Fi systems. We believe that by educating people about these important topics, we can help them make informed decisions and improve the state of cybersecurity for everyone.
The educational videos provided with KJ are designed to grow with your knowledge and take you from a beginner to an advanced level. As your understanding of cybersecurity and Wi-Fi vulnerabilities evolves, our educational content will evolve with you. Our commitment to education goes beyond just the initial product launch.

We will continually update and improve our educational videos to ensure that you have access to the most up-to-date information and insights in the field. With KJ, you can be confident that you are not only getting a highly durable and effective device, but also a valuable educational resource that will help you stay informed and protected in an ever-changing technological landscape.”

KJ is not just an educational tool, but also a valuable asset for cyber security professionals. The device’s robust construction and advanced features make it ideal for use in real-world scenarios. Whether you’re a seasoned professional or just starting out, KJ provides a powerful tool for testing the security of Wi-Fi networks and improving your overall understanding of cybersecurity. The educational videos and resources included with the device make it a comprehensive solution for individuals looking to advance their careers in the field. By using KJ, you can stay ahead of the curve and gain a competitive edge in the fast-paced world of cybersecurity.
T-SHIRTS

KAOS TSHIRTS are made with the highest quality 100% cotton to ensure maximum comfort and durability. The natural breathability and softness of the fabric make our t-shirts perfect.
Kaos t-shirts also feature designs on both the front and back.
Well, let’s be honest. There’s not a lot to say about T-shirts, is there? They’re pretty straightforward. No fancy features, no complex technology (not like KJ). They’re just T-shirts. But that’s not to say they’re not important. In fact, T-shirts are a staple of any wardrobe, and they can say a lot about your personal style.
Our T-shirts may not have all the features and technology of KJ’s devices, but they’re still a great way to represent the cult’s philosophy and show your support. Plus, they’re made from high-quality materials and feature unique designs . So even though they may seem simple, our T-shirts are still an important part of the KJ line.

STRETCH GOALS

If the stretch goals are met, all of the device features will be included in each unit shipped, with the exception of the “First Batch” Reward. Additionally, customers will have the opportunity to select their preferred color through our pledge manager.

REWARDS

Please note that the devices in the “First batch”, which will be the first to ship, do not include any of the “Stretch Goals” features nor the page with all the names of the backers. However, we want to assure you that all devices in the first batch are fully functional and have been extensively tested to ensure their quality. While there may be some minor aesthetic imperfections on the edges of the devices, please be assured that they will not affect the overall functionality of the product.

TIMELINE – PROJECT PLAN

SHIPPINGS

Our shipping is available worldwide and the cost will be added through our pledge manager after the campaign. Our goal is to keep any potential additional costs to a minimum. However, due to factors such as shipping volume, we are unable to determine the exact shipping cost at this time. If we are able to ship items in larger volumes, we may be able to negotiate lower shipping rates, which we will then pass on to you to help minimize any additional expenses. At this time, you can also verify your rewards, address, and add any additional items. Please be aware that eventual local taxes, duties, and VAT are not included in our prices and will be subject to the specific laws and regulations of your country.
Closer to the shipping date on our website, we will ask you to pay the shipping fee separately via our pledge manager. Due to the unpredictability of shipping prices, we cannot provide an exact delivery cost at this time.
Currently, we anticipate shipping prices to range between 10€ to 35€, depending on the shipping area and the number of products. We are not profiting from the shipping costs and will work to optimize the process for the lowest prices and fastest delivery times.
MANIFESTO

The text highlights the dangers of blindly accepting oversimplifications from corporations and lawmakers and urges us to develop critical thinking skills to become active participants in shaping the course of the digital age. We envision a future where we use technology as a tool for understanding and creation, and where hackers are seen as symbols of creativity and problem-solving. We are called upon to reclaim our power by breaking free from ignorance and becoming active participants. Let us hack our way out and shape the future ourselves.
Many of the laws and regulations related to cybersecurity are born out of a general lack of knowledge and understanding about the technology involved. This can lead to well-intentioned laws that end up being impractical, ineffective, or even harmful.
One example of this is the European Cookie Law. This law was designed to protect the privacy of internet users by requiring websites to inform users about the use of cookies and obtain their consent before placing them. However, the law has been criticized for being too strict and not accounting for the essential role cookies play in modern internet browsing. Many websites rely on cookies for basic functionality, such as remembering user preferences or keeping track of items in a shopping cart.
The cookie law is an example of how legislation can be created in response to a perceived risk without a full understanding of the technology involved. In some cases, these laws can actually increase the risk to users by creating a false sense of security or by discouraging the use of effective security measures.

Another example of this lack of understanding is the debate around encryption and backdoors. The FBI’s request to Apple to create a backdoor to access a locked iPhone was based on the belief that such a backdoor would help prevent terrorism and other crimes. However, the reality is that any backdoor created for law enforcement would also be accessible to hackers and other malicious actors. This would compromise the privacy and security of all users, not just those targeted by law enforcement.
The debate around encryption is not just about the technology itself, but about the values and principles that underpin our society. It is a question of whether we value privacy and security, or whether we prioritize law enforcement and surveillance. It is important for policymakers and the masses to have a deep understanding of the technology and its implications, as well as the broader social and ethical implications of their decisions.
Imagine a world where people take control of their digital lives, where technology is not just a mysterious black box but a tool for empowerment and positive change. Sadly, that’s not the reality for many of us today. Most people use technology without fully understanding how it works or the risks and opportunities it presents. This can leave us vulnerable to malicious actors, and make it harder for us to make informed decisions about our digital lives.

We hope that our device will inspire people to take an active role in shaping the future. By being more aware of the risks and opportunities of cybersecurity, people can make better decisions and take control of their digital lives. We believe that this will lead to a more informed and empowered society, by promoting cyber security education, we hope to prevent these kinds of misguided policies and ensure the benefit of all.
The world is changing faster than ever before, and tech is at the forefront of this transformation. In this digital age, ignorance is not bliss. In fact, it can be downright dangerous. The lack of knowledge and understanding about the digital world can lead to bad decisions, misguided policies, and even threats to our security and privacy.
We have the power to change this. We can educate ourselves and each other, and by doing so, we can shape a better future, and use this knowledge to make informed decisions and create positive change.
We must remember that technology is not just a tool, it is a powerful force that can shape the world around us. If we don’t take the time to understand it, we risk being left behind, or worse, falling prey to its negative consequences. Let’s shape a future that benefits us all. By educating ourselves and each other about technology, we can build a more informed, empowered, and connected world.
We envision a future where people are more conscious about the power of technology and the risks that come with ignorance and lack of knowledge. That’s why we have designed a device to teach about cyber security. We believe that by educating people about cyber security, we can create a more conscious society that is better equipped to navigate the challenges of the digital age.

TEAM

CONNECT WITH US
Thank you for arriving here, if you did, you like what we made (we hope). Please help us by sharing this page on social media, we’ll really appreciate it. and follow us on our Socials @KAOSJAMMER on Facebook, Youtube, Tiktok and Instagram.

PRESS

We have a dedicated area, with press release images, video, and blog updates at:
Dedicated Google Drive with Press materials:
https://drive.google.com/drive/u/1/folders/1EMZf_JRG_Ed6Rbw9DMYWde_ZlngguW-R




Risks and challenges
In order to mitigate any potential risks, we have taken all necessary steps to thoroughly test every aspect of our product and production process. We have produced a small batch of units to test for any possible issues and address any problems before moving forward with mass production. After multiple rounds of testing, we are confident in our ability to produce and deliver the product in large quantities. While an increase in the number of orders or completion of stretch goals may present challenges, we have conducted thorough research and analysis to ensure that we are equipped to meet any demands that may arise. Our product has undergone multiple rounds of testing during production, and we have optimized our production line and quality control measures to ensure that the final product is of the highest quality. We have successfully established agreements with multiple suppliers to source all the required components for the assembly process. Additionally, we have tested the logistics in multiple countries to anticipate and address any potential issues that may arise during shipping. We are confident that we will be able to produce and deliver the products within the timeframe that we have predicted. In summary, our meticulous attention to detail throughout every step of the production process has given us the confidence to fulfill our promises.
Environmental commitments
Long-lasting design
The device has been engineered with longevity in mind and boasts exceptional durability, including drop-proof and impact-resistant features to ensure sustained usage over time.
Sustainable materials
The device is constructed using eco-friendly materials such as eco-leather and recyclable components.
Sustainable Distribution
We implemented measures to minimize our shipping packages without compromising the safety and security of the product during transit. This not only benefits the environment by reducing waste that may end up in landfills, but also provides cost savings that we are passing on to our backers. We believe that this is a responsible and sustainable approach that aligns with our company’s values and goals.